Introduction
Blockchain networks operate without a central authority, yet they still need a reliable way to verify transactions, protect data, and maintain agreement across thousands of computers. Cryptocurrency algorithms make this possible.
These algorithms are sets of mathematical rules that determine how blockchain networks process transactions, secure information, and coordinate activity between participants. They define how blocks are created, how transactions are verified, and how the network reaches consensus on the current state of the ledger.
Different cryptocurrencies use different combinations of algorithms depending on their design goals. Some prioritize security and decentralization, while others focus on scalability or energy efficiency.
Understanding how cryptocurrency algorithms work helps explain the technology behind blockchain systems and why different networks operate in different ways.
Key Takeaways
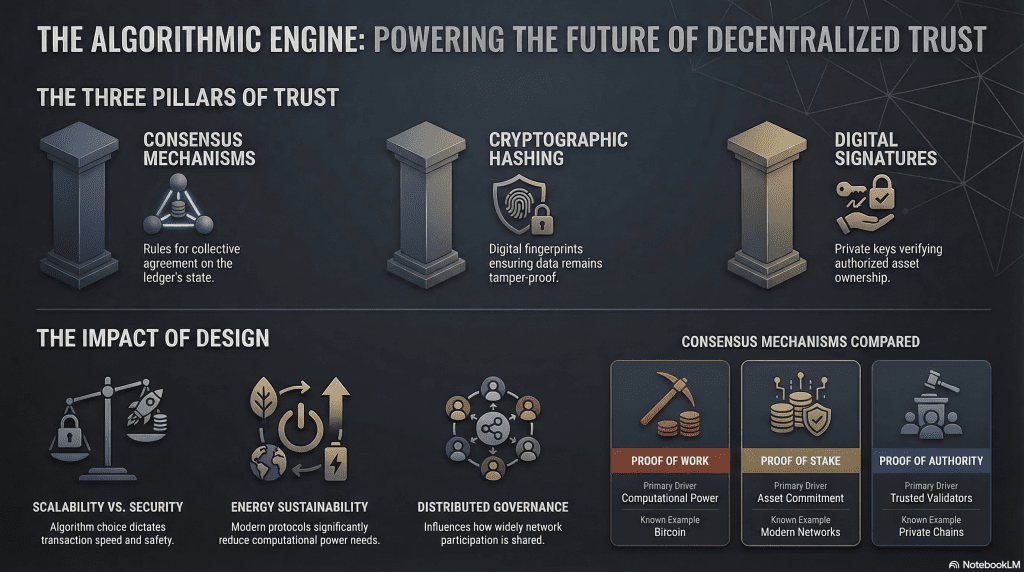
- Cryptocurrency algorithms are mathematical rules that allow blockchain networks to operate securely without central control.
- Consensus algorithms enable decentralized networks to agree on the state of the blockchain.
- Hashing algorithms protect transaction data and help maintain the integrity of blocks.
- Cryptographic signature algorithms verify ownership of digital assets.
- Algorithm design can influence network security, transaction speed, energy usage, and decentralization.
Disclaimer: Some links on this website are affiliate links. That means if you click and make a purchase, we may earn a small commission at no extra cost to you. The views expressed here are not official statements from any outside company.
What Is a Cryptocurrency Algorithm?
A cryptocurrency algorithm is a set of computational rules used to manage and secure blockchain operations. These algorithms determine how transactions are verified, how blocks are created, and how network participants agree on the validity of data.
In traditional financial systems, a central authority such as a bank maintains transaction records and verifies transfers. Blockchain networks operate differently. Instead of relying on a central institution, they use algorithms to coordinate activity across distributed computers known as nodes.
These algorithms help perform several important functions within a blockchain network:
- validating transactions before they are recorded
- linking blocks of data into a chronological chain
- protecting information through cryptographic techniques
- coordinating agreement across decentralized participants
Without these algorithmic rules, a blockchain network would not be able to maintain a consistent and secure ledger.
Cryptocurrency algorithms are therefore essential to the operation of blockchain technology. They allow decentralized systems to function reliably while reducing the need for centralized oversight.
Types of Cryptocurrency Algorithms
Cryptocurrency algorithms perform different roles within a blockchain network. While they work together to maintain the system, they can generally be grouped into three main categories based on their function.
These categories include:
- Consensus algorithms, which allow decentralized networks to agree on the state of the blockchain
- Cryptographic hashing algorithms, which protect transaction data and maintain block integrity
- Cryptographic signature algorithms, which verify ownership and authorize transactions
Each type of algorithm addresses a specific challenge in decentralized systems. Consensus mechanisms coordinate agreement among participants, hashing algorithms secure the blockchain’s data structure, and signature algorithms confirm that transactions are authorized by the correct users.
Understanding these categories helps clarify how blockchain networks maintain security and reliability without relying on centralized control.

Consensus Algorithms
Consensus algorithms are responsible for helping decentralized networks agree on the current state of the blockchain. Because blockchains operate across many independent nodes, the system must have a method for determining which transactions are valid and which blocks should be added to the chain.
Consensus mechanisms provide this coordination. They establish rules that participants follow when validating transactions and confirming new blocks.
Different blockchain networks use different consensus models depending on their design priorities, such as security, efficiency, and decentralization.
Proof of Work (PoW)
Proof of Work is one of the earliest and most widely recognized consensus mechanisms. In PoW systems, participants known as miners compete to solve complex computational puzzles.
The first miner to solve the puzzle earns the right to add a new block of transactions to the blockchain. The solution is then verified by other nodes in the network.
Bitcoin uses Proof of Work, and the process requires significant computing power.
Proof of Stake (PoS)
Proof of Stake uses a different approach to transaction validation. Instead of relying on computational work, validators are selected based on the amount of cryptocurrency they commit, or “stake,” within the network.
Validators who participate honestly may receive rewards, while malicious behavior can result in penalties that reduce their staked assets.
Many newer blockchain networks use PoS because it generally requires less computational power than Proof of Work.
Delegated Proof of Stake (DPoS)
Delegated Proof of Stake introduces a voting system into the validation process. Token holders vote to elect a smaller group of delegates who are responsible for confirming transactions and maintaining the blockchain.
This model can increase transaction throughput, although it introduces a different governance structure compared to other consensus systems.
Proof of Authority (PoA)
Proof of Authority is often used in private or permissioned blockchain environments. In PoA systems, a limited number of trusted validators are responsible for confirming transactions.
Because validators are known entities, this approach can allow faster transaction processing, although it relies on a level of centralized trust.

Cryptographic Hashing Algorithms
Cryptographic hashing algorithms are used to protect and organize data within a blockchain. These algorithms convert input data into a fixed-length string of characters known as a hash.
Each transaction included in a block is processed through a hashing function. The resulting hash acts like a digital fingerprint for that data. Even a small change to the original input will produce a completely different hash output.
This property helps ensure that blockchain records cannot be altered without detection. Because each block contains the hash of the previous block, changing one block would require recalculating every block that follows it. This structure is what creates the blockchain’s tamper-resistant design.
Several hashing algorithms are commonly used in cryptocurrency networks.
SHA-256
SHA-256 (Secure Hash Algorithm 256-bit) is one of the most widely known hashing algorithms in the cryptocurrency ecosystem. It is used by the Bitcoin network as part of its Proof of Work mining process.
The algorithm converts transaction data into a 256-bit hash, helping secure the blockchain and verify new blocks during mining.
Scrypt
Scrypt is another hashing algorithm used by cryptocurrencies such as Litecoin and Dogecoin. It was designed to be more memory-intensive than SHA-256, which can make mining less dependent on specialized hardware.
This design was intended to encourage broader participation in mining during the early development of these networks.
Equihash
Equihash is used by the Zcash network and was designed with memory-hard properties that reduce the advantage of certain types of specialized mining equipment.
This approach was introduced to help maintain more distributed participation in the mining process.
X11
X11 is a chained hashing algorithm used by the Dash cryptocurrency. Instead of relying on a single hashing function, it combines eleven different cryptographic hashing algorithms in sequence.
The design aims to add additional layers of complexity to the mining process.

Cryptographic Signature Algorithms
Cryptographic signature algorithms are used to verify ownership and authorize transactions on a blockchain network. These algorithms rely on public-key cryptography, where each user controls a pair of cryptographic keys: a private key and a public key.
The private key is used to sign transactions, while the public key allows other participants in the network to verify that the transaction was authorized by the correct owner.
When someone sends cryptocurrency, their wallet software uses the private key to create a digital signature. Nodes in the network can then verify this signature using the corresponding public key. If the signature is valid, the transaction can be included in a block.
This process allows blockchain networks to confirm ownership of digital assets without exposing private keys or relying on a central authority.
Two commonly used signature algorithms in blockchain systems include the following.
Elliptic Curve Digital Signature Algorithm (ECDSA)
ECDSA is widely used in cryptocurrency networks, including Bitcoin. It allows users to sign transactions securely while keeping private keys confidential.
The algorithm is based on elliptic curve cryptography, which provides strong security with relatively small key sizes.
Ed25519
Ed25519 is a modern digital signature algorithm used in several blockchain systems. It is designed for high performance and strong security.
Some networks use Ed25519 because it can provide faster signature verification and simpler implementation compared with earlier signature algorithms.

Why Cryptocurrency Algorithms Matter
Cryptocurrency algorithms influence how blockchain networks operate in several important ways. The design of these algorithms affects security, performance, and how decentralized a network can remain.
Because different blockchains use different combinations of algorithms, their capabilities and limitations can vary.
Security
Algorithms play a central role in protecting blockchain networks from tampering and fraud. Cryptographic hashing ensures that transaction data cannot be easily altered, while digital signatures verify that transactions are authorized by the correct owners.
Consensus mechanisms also contribute to security by requiring network participants to follow defined validation rules before new blocks are added to the chain.
Scalability
Scalability refers to how efficiently a blockchain can process transactions as network usage grows. The consensus mechanism used by a network often influences how quickly transactions can be validated and confirmed.
Some algorithm designs focus on maximizing decentralization and security, while others aim to increase transaction throughput.
Energy Consumption
Different consensus mechanisms require different levels of computational resources. Proof of Work systems rely on intensive computing power to solve cryptographic puzzles, which can result in higher energy usage.
Alternative mechanisms such as Proof of Stake use different validation methods that typically require less computational work.
Decentralization
Algorithms also influence how widely network participation can be distributed. In some systems, validation can be performed by many independent participants, while in others the process may involve a smaller set of validators.
The balance between decentralization, efficiency, and security often depends on the specific algorithm design chosen by the blockchain network.

Future Trends in Cryptocurrency Algorithms
Blockchain technology continues to evolve, and research into new cryptographic and consensus mechanisms is ongoing. Developers and researchers are exploring ways to improve security, scalability, and efficiency while maintaining the decentralized nature of blockchain networks.
Energy-Efficient Consensus Mechanisms
One area of focus is reducing the energy requirements associated with blockchain operations. Proof of Stake and related models were developed in part to address the energy demands of Proof of Work systems. Some newer blockchain networks are also experimenting with hybrid consensus approaches that combine elements of different mechanisms.
Quantum-Resistant Cryptography
Another area of research involves cryptographic methods designed to remain secure in the presence of future quantum computing capabilities. Quantum computers could potentially weaken some current cryptographic systems, so researchers are investigating alternative algorithms that may provide stronger resistance to such threats.
Improved Scalability Mechanisms
As blockchain networks grow, handling large volumes of transactions becomes increasingly important. New algorithm designs and consensus models aim to improve throughput while maintaining network security and reliability.
These developments reflect ongoing efforts to refine the underlying technologies that support blockchain systems.

Conclusion
Cryptocurrency algorithms form the technical foundation of blockchain networks. They define how transactions are verified, how data is protected, and how decentralized systems maintain agreement without relying on central authorities.
Consensus mechanisms, hashing algorithms, and cryptographic signature systems each play a specific role in the operation of blockchain networks. Together, these algorithms allow cryptocurrencies to function as distributed systems where participants can exchange and verify digital assets securely.
Understanding these mechanisms provides insight into how blockchain technology works and why different cryptocurrency networks may operate in different ways.

Frequently Asked Questions
What is a cryptocurrency algorithm?
A cryptocurrency algorithm is a set of mathematical rules that governs how a blockchain network verifies transactions, secures data, and maintains consensus among participants.
What algorithm does Bitcoin use?
Bitcoin uses the SHA-256 hashing algorithm as part of its Proof of Work mining process.
What is the difference between Proof of Work and Proof of Stake?
Proof of Work requires computational effort from miners to validate transactions and create blocks. Proof of Stake selects validators based on the amount of cryptocurrency they commit to the network.
Are cryptocurrency algorithms secure?
Cryptocurrency algorithms are designed to provide strong security through cryptographic techniques and consensus rules. However, overall network security also depends on implementation, participation levels, and system design.
Can blockchain operate without algorithms?
No. Blockchain networks rely on algorithms to validate transactions, protect data, and coordinate agreement among decentralized participants.